Login Möglichkeiten/en: Unterschied zwischen den Versionen
Weitere Optionen
Faha (Diskussion | Beiträge) Die Seite wurde neu angelegt: „If the AAD is now set up as the Authentication Provider for HITGuard, users can log in to HITGuard via Single Sign On (see figure below).“ |
Faha (Diskussion | Beiträge) Die Seite wurde neu angelegt: „The prerequisite is that a user exists in HITGuard whose email address matches the email address used to log in to AAD. This is because: When logging in via AA…“ |
||
| Zeile 24: | Zeile 24: | ||
If the AAD is now set up as the Authentication Provider for HITGuard, users can log in to HITGuard via Single Sign On (see figure below). | If the AAD is now set up as the Authentication Provider for HITGuard, users can log in to HITGuard via Single Sign On (see figure below). | ||
The prerequisite is that a user exists in HITGuard whose email address matches the email address used to log in to AAD. This is because: When logging in via AAD for the first time, this is used to connect the AAD user with the HITGuard user. Subsequently, the email address of the HITGuard user can be changed if necessary. | |||
Version vom 16. November 2021, 08:05 Uhr
HITGuard supports the Authentication Provider Active Directory (AD), Azure Active Directory (AAD), Active Directory Federation Services (ADFS) and OpenIdProvider.
Active Driectory
The Active Directory is the only Authentication Provider that can be set at runtime of HITGuard. It can be configured by administrators and experts in the Global Settings.
More about Active Directory configuration can be found at "Administration → Global Settings → LDAP".
Azure Active Directory
To configure the Authentication Provider AAD or ADFS, the "appsettings.production.json" file of HITGuard must be modified. This file is located in the root directory of the installation folder.
In the AzureAd section, the following entries need to be customized to your Azure app:
- "Activated": true,
- "Instance": "https://login.microsoftonline.com/",
- "HITGuardBaseUrl": "https address where your HITGuard instance is accessible",
- "ClientId": "your-clientId-guid",
- "TenantId": "your-tententId-guid",
- "ClientSecret": "your-tententId-guid",
Single Sign On (SSO)
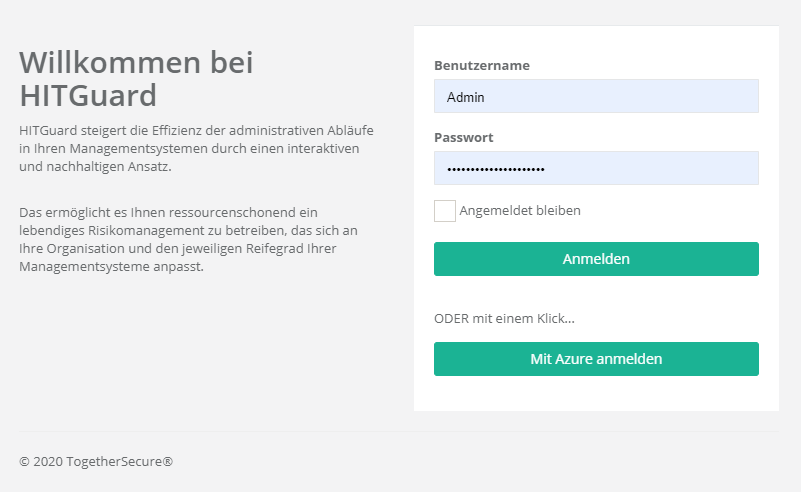
If the AAD is now set up as the Authentication Provider for HITGuard, users can log in to HITGuard via Single Sign On (see figure below).
The prerequisite is that a user exists in HITGuard whose email address matches the email address used to log in to AAD. This is because: When logging in via AAD for the first time, this is used to connect the AAD user with the HITGuard user. Subsequently, the email address of the HITGuard user can be changed if necessary.
Active Directory Federation Services
Um ein ADFS zu konfigurieren müssen sie ähnlich wie beim Azure Active Directory vorgehen und im "appsettings.production.json" File die Einträge
- "MetadataAddress": "https://adfs.yourcompany.com/FederationMetadata/2007-06/FederationMetadata.xml",
- "Wtrealm": "https://www.hitguard.com/"
konfigurieren.
Single Sign On (SSO)
Siehe Azure Active Directory (AAD) SSO.
OpenID Connect Provider
Um einen OpenID Connect Provider einzurichten, muss wie bei AAD bzw. ADFS vorgegangen werden und in der Datei "appsettings.production.json" Einstellungen hinzugefügt werden. Dieses Protokoll ist sehr variabel und bietet umfassende Einstellungsmöglichkeiten. Eine Erklärung würde diesen Rahmen sprengen. Wenn Sie Fragen zur Einstellung eines OpenID Connect Providers haben, melden Sie sich unter "office@togethersecure.com".